Level Finance is a decentralized finance (DeFi) platform operating on the BNB Chain that offers users the ability to trade perpetual markets in a non-custodial and decentralized manner. The platform focuses on providing unique risk management features and innovative liquidity solutions, aiming to create an efficient, transparent, and secure financial ecosystem. However, its advanced architecture also exposes vulnerabilities that can be exploited by malicious actors. In this hack analysis, we will explore the Level Finance hack, where $1.1 million in referral rewards were stolen, emphasizing the critical role of security measures and on-chain monitoring in the DeFi space.
Hack Impact
The Level Finance hack significantly affected the platform and its users, as the attacker managed to steal $1.1 million in referral rewards. This breach undermined trust in Level Finance and raised concerns about the security of similar DeFi platforms. Additionally, the LVL token price crashed by 65% due to the attacker’s actions, although it later mostly recovered. This price fluctuation negatively impacted investor and trader confidence, potentially affecting trading volume and market liquidity.

Level Finance: Hack Explained
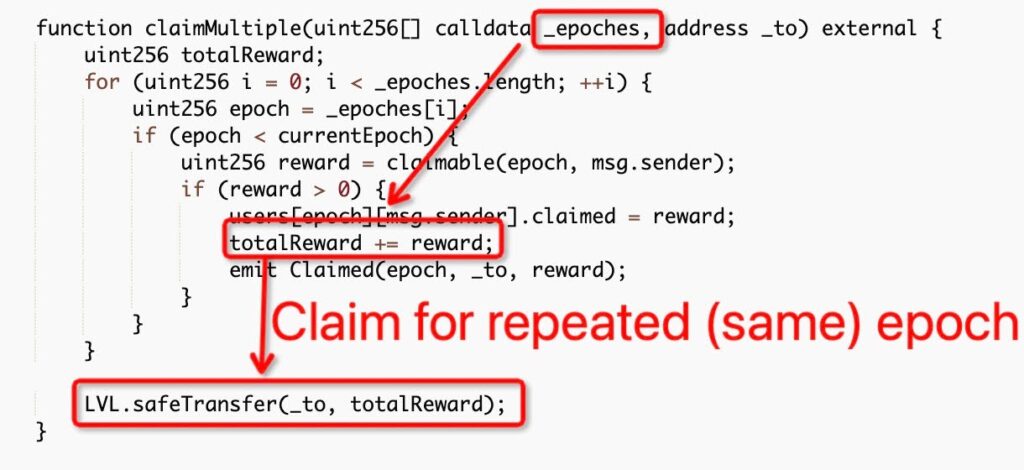
The Level Finance hack occurred due to a bug in the LevelReferralControllerV2 contract. The contract contained a function called “claimMultiple,” which was designed to allow users to claim their referral rewards for multiple epochs. However, the function lacked a critical check that would prevent a user from claiming rewards for the same epoch multiple times. The attacker exploited this vulnerability to steal a large amount of LVL tokens, which they later converted into BNB.
Here is the Break down of the Attack:
Understanding the Vulnerable Function
The “claimMultiple” function is like a rewards counter at a store, where customers can redeem their earned points for rewards. However, the counter has a flaw: it doesn’t check if a customer has already claimed their reward for the same period (epoch). This allows customers to claim the same reward multiple times.
Preparing the Attack
The attacker, acting like a cunning customer, first created many referrals to increase their reward tier (the more referrals, the higher the rewards). Next, they used flash loans to perform dozens of swaps, simulating genuine trading activity and increasing their reward points further.
Exploiting the Vulnerability
The attacker visited the flawed rewards counter (the “claimMultiple” function) and claimed referral rewards for the same epoch multiple times, taking advantage of the missing check. So, this allowed them to drain a large number of LVL tokens from the Level Finance platform.
Cashing Out
After accumulating 214k LVL tokens, the attacker swapped them for 3,345 BNB, equivalent to approximately $1 million at the time of the hack. This process is akin to the cunning customer exchanging their illegitimately obtained rewards for cash at the store.
Recommendations for Enhanced Security
To prevent similar attacks from occurring in the future, it is crucial to implement robust technical mitigation measures. So, here are some recommendations to address the vulnerability in the LevelReferralControllerV2 contract:
Add a Check for Reused Epochs
Modify the “claimMultiple” function to include a check that prevents users from claiming rewards for the same epoch more than once. You can achieve this by adding a conditional statement that verifies if the user has already claimed rewards for a specific epoch before processing their claim.
Example code addition:
require(users[epoch][msg.sender].claimed == 0, “Reward already claimed for this epoch”);
Improve Auditing and Testing
Enhance the auditing process by working closely with reputable security firms, ensuring a comprehensive review of the smart contracts. Implement thorough testing, including edge cases and stress tests, to identify any potential vulnerabilities before deployment.
Monitor On-Chain Activity
Implement robust on-chain monitoring systems to detect suspicious activities and potential threats in real-time. This can help in identifying and mitigating attacks before they cause significant damage.
Transaction Analysis
Exploiter’s Address: 0x70319d1c09e1373fc7b10403…
This is the address used by the attacker to execute the hack and receive the stolen LVL tokens. By examining the transaction history of this address, we can trace the steps taken by the attacker, including the preparation for the attack and the subsequent token swaps.
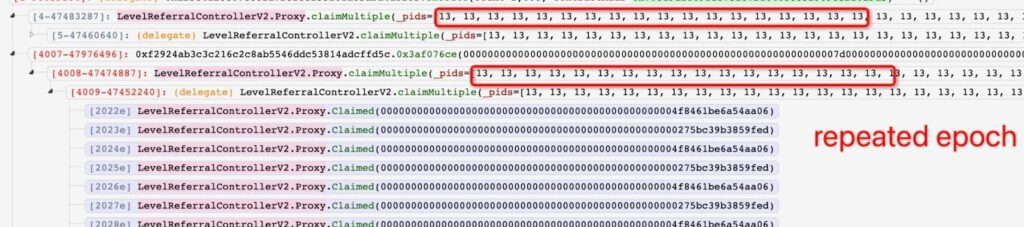
Hack Transaction: 0xe1f25704…
shows how the attacker used the claimMultiple function to exploit the vulnerability and drain LVL tokens. Then on analyzing, the transaction reveals that the attacker repeatedly claimed referral rewards for the same epoch, leading to a large transfer of LVL tokens to their address.
LevelReferralControllerV2 Contract: 0x977087422C008233615b572…
This contract contains the vulnerable claimMultiple function that the attacker exploited. By analyzing the contract’s code and interactions with other addresses, we can better understand the nature of the vulnerability and its implications.
Drained LVL Tokens and Swaps:
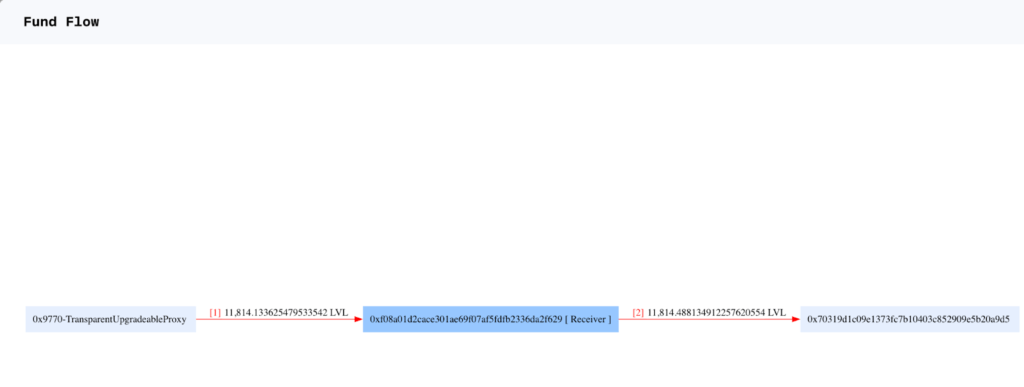
After successfully exploiting the vulnerability, the attacker drained 214k LVL tokens to their address. They then proceeded to swap the LVL tokens for 3,345 BNB, worth approximately $1 million at the time of the hack. The swapping of tokens contributed to the temporary crash in the LVL token price.
Fund Flow
Conclusion
The Level Finance hack highlights the importance of robust security measures and thorough auditing processes for decentralized finance platforms. Despite being a sophisticated DeFi platform with innovative features, Level Finance fell victim to a $1.1 million hack due to a vulnerability in the LevelReferralControllerV2 contract. This incident demonstrates that even well-designed platforms can face significant risks without proper security checks and balances.
As DeFi platforms continue to grow in popularity, it is crucial for developers and project teams to prioritize the security of their smart contracts and to learn from incidents like the Level Finance hack. Implementing robust technical mitigations, conducting comprehensive audits, and engaging the community can significantly reduce the risk of security breaches and ensure a safer environment for users.
In light of this incident, we strongly recommend projects to get their smart contracts audited by reputable security firms such as BlockApex . A thorough audit conducted by experienced professionals can help identify and address vulnerabilities before they can be exploited by malicious actors, ultimately safeguarding the integrity of the platform and its users’ assets.
By taking these important steps, DeFi platforms can continue to innovate and thrive while ensuring the security and trust of their users.
Explore further Hack Analysis: