We live in a world today where people are well aware of the fact that companies fetch users’ data to provide value against it. Unfortunately, this commission was left behind, as now the data is being used in several ways that the users never agreed upon! Meaning that consumer privacy concerns were overlooked. Now, data is used without consent.
Backlog Of The Internet:
The internet we see today is the evolution of three decades worth of innovation. From a single-user perspective, accessibility, or a business perspective, the internet is bombarded with information daily.
But, the internet started its journey when launched worldwide in 1989. At that time internet was famously known as Web 1.0. The websites present on the internet were basic and played the role of read-only and information-gaining websites.
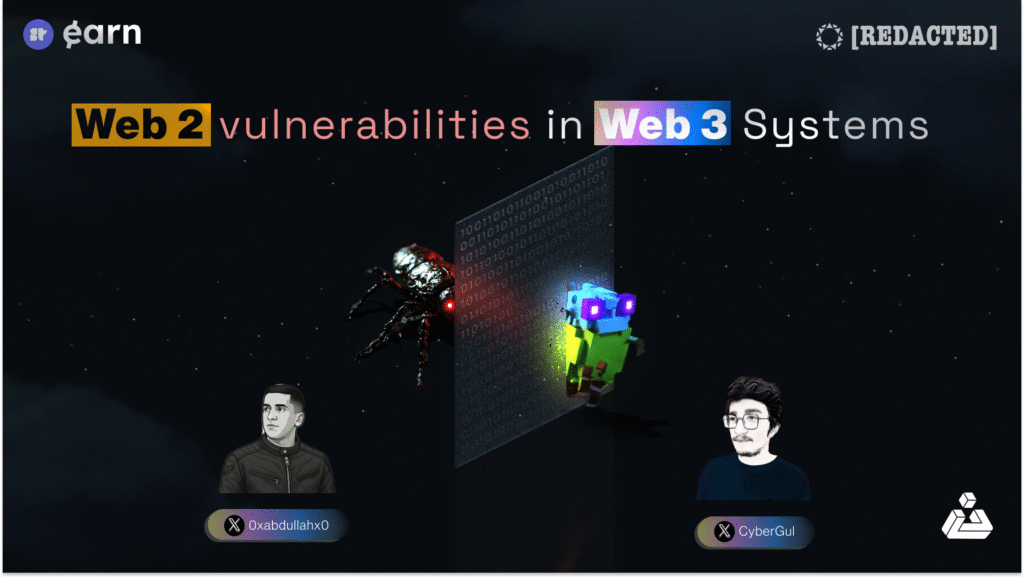
When the dot-com bubble burst, the technology modifications accelerated, and web 1.0 transformed into web 2.0. User-generated content took a boom, that allowed users to interact with the content and share their thoughts. But, the happiness wasn’t long-lived, the people soon realized that their information is being tracked and used for target marketing. This arose the problem – centralization. Centralization is a phenomenon, where all the decision-making powers lie in the top hierarchy. Moreover, the misuse of users’ information increased resulting in several consumer privacy and data breach issues.
The last few years have resulted in consumer privacy and data breach issues. Those issues have made the users conscious and ambiguous about the data on the internet. Most of the users are not yet informed about the importance of their data and how immorally it is being used.
In response, several laws were made protecting consumers’ privacy but all they did was checking off some boxes for businesses. So, what should be done to prevent data breach which is massively being done?
Well, Web 3.0 seems to solve these problems! Let’s wade in to discover!
Is Web 3.0 The Cure For Consumer Privacy & Data Breach?
The internet fundamentally needs to build and support a healthier relationship between companies and their consumers’ privacy. To cater to that need a new evolution of the internet comes into the picture called Web 3.0 – firstly coined by Gavin Wood (Co-Founder of Ethereum & Founder of Polkadot).
So, how Web 3.0 is curing consumer privacy and data breach issue? Simple, through Blockchain Technology. Blockchain technology supports decentralization, where the user is not bound by single/multiple authoritative entities.
Let’s dive in and see how web 3.0 is helping the internet to eradicate the issue of consumer privacy & data breach.
1. Web 3.0 An Equitable Space:
Web 3.0 provides a decentralized infrastructure where it provides privacy protection to every individual user. The platforms are protected algorithmically. By nature, blockchains are protected and no one can make amendments to the code, making them highly secure. By enabling individuals to be sovereign, web 3.0 is said to be an equitable space.
2. User Own Their Data:
Since users in the current paradigm are facing the problem of data breaches, blockchain technology allows users to have ownership over their data. Blockchain holds all the records making it secure and also transparent.
3. Advanced-Data Breach Policy:
Web 3.0 solves the data breach issue by allowing every individual to know how their information is being used. The users will still be able to share their data but will exactly know how their data is being utilized. The companies benefiting from the data would also be transparent, allowing the users to revoke their information any time they want.
4. Blockchain Technology is Less Hackable:
There have been more than 98.2 million individuals affected by data breaches in 2021. Year over a year these kinds of attacks are being common. Blockchain technology provides a protective layer over the information of every user. Blockchain is computability designed to be less hackable. Since the chain is being reviewed constantly, the completion of an attack is rarely possible.
But the story doesn’t end here! Why? Because there are still years for blockchain technology to be adopted throughout the world. Meanwhile, the practices done in web 2.0 could be enhanced to give a better experience to the user. How? Let’s explore and find out!
1. Transparency Is The Key:
Companies involved in consumer privacy and data breach activities should be open and transparent about it. The more they share, the more they would likely gain the trust of people. It would also summon people to be more careful about putting their information on the internet.
2. Upgrade The Value Exchange Policy:
Existing in a world where every individual enjoys a win-win situation is rare. Even now there are not many businesses that incentivize people to share their information. If they could communicate through their value exchange policies what value they drive from the data, surely users would grant access to their information.
In a Nutshell:
The revolution of the internet brought a lot of advancements to the world. The internet became a breakthrough for a billion people around the world. But it also brought various problems along. To combat those issues web 3.0 is on its way and would most likely with its blockchain technology resolve issues.