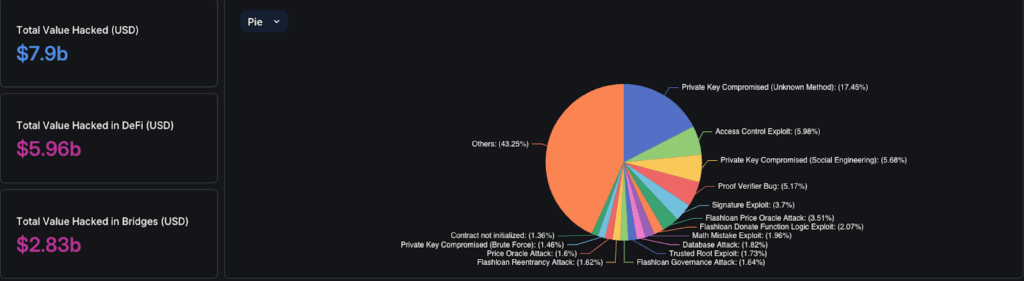
Smart contracts are the backbone of the blockchain ecosystem, powering decentralized applications (DApps) and handling transactions worth millions of dollars. However, with their immense power comes significant vulnerability. Code errors, logic flaws, and security breaches in smart contracts can result in devastating financial losses and irreparable reputational damage. In 2023 alone, Web3 businesses lost nearly $400 million due to smart contract exploits, many of which were attributed to unaudited or poorly audited code. This underscores the urgent need for thorough audits to mitigate risks and manage smart contract audit costs effectively. Investing in comprehensive audits can prevent costly exploits and safeguard both financial assets and reputations.
Smart contract audits are essential to ensure the security, reliability, and efficiency of these self-executing codes. Audits involve a meticulous examination of the contract’s code and architecture to identify smart contract vulnerabilities and inefficiencies before deployment. By leveraging a combination of automated tools and expert manual reviews, auditors can provide a comprehensive assessment, safeguarding assets and instilling confidence in blockchain technology.
In this article, we will explore the indispensable tools for auditing smart contracts. From initial reconnaissance to final reporting, these tools are crucial for every step of the audit process, helping you deploy secure and robust smart contracts.
The Smart Contract Audit Journey: Ensuring Security from Start to Finish
A comprehensive smart contract audit involves several stages, each requiring specialized tools to identify, analyze, and document vulnerabilities. Here’s an overview of the typical audit process and the tools used at each step.
Initial Reconnaissance: Gathering Crucial Insights
The first step in a smart contract audit is reconnaissance, where auditors gather information about the contract, reading documentation/whitepaper for understanding business logic, its functionality, and its deployment environment. This phase involves understanding the contract’s purpose, identifying dependencies, and examining its architecture.
Tools for Reconnaissance
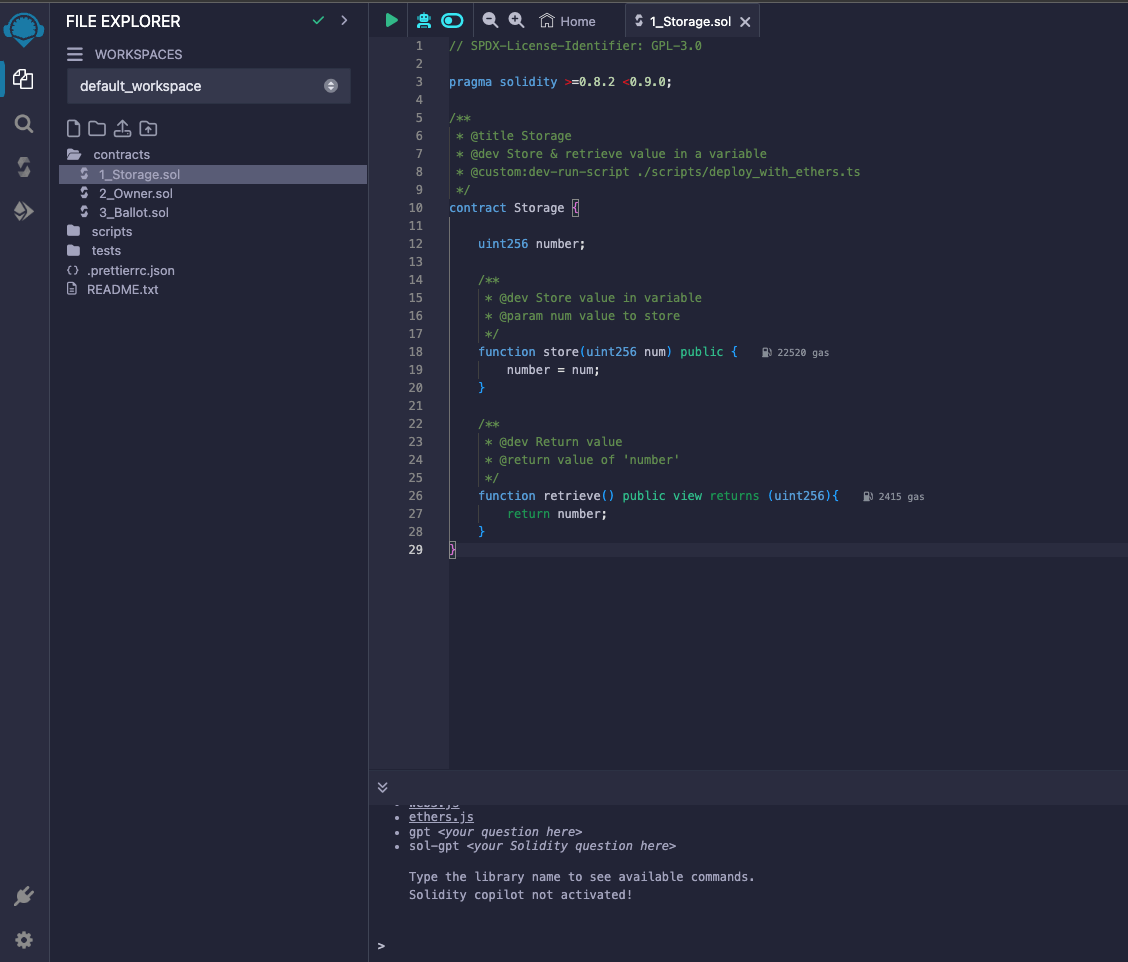
- Remix IDE: An open-source Solidity IDE that offers a powerful environment for coding, testing, debugging, and deploying smart contracts. Its integrated features, plugin manager make it a preferred choice for initial contract analysis.
- Visual Studio Code (VSCode): A leading code editor launched in 2015, maintained by Microsoft. VSCode offers extensive support for Solidity developers through various extensions and plugins, providing an immersive experience for developing decentralized applications.
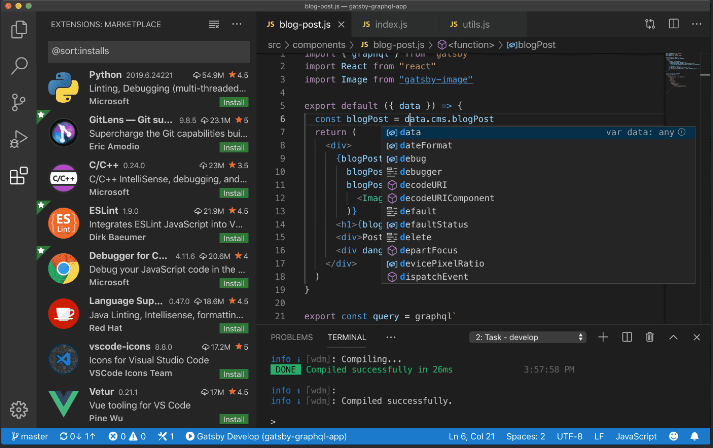
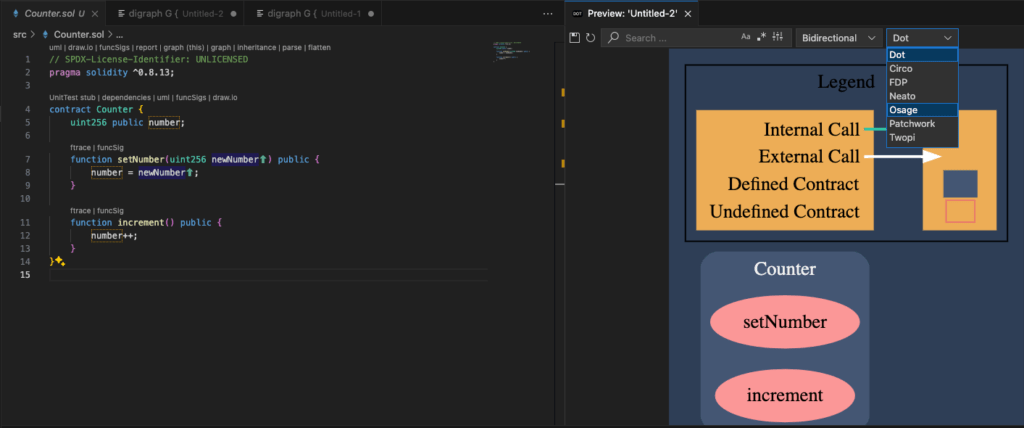
- Solidity Visual Auditor (SVA): This tool provides a visual representation of smart contracts, helping auditors understand the structure and flow of the code.
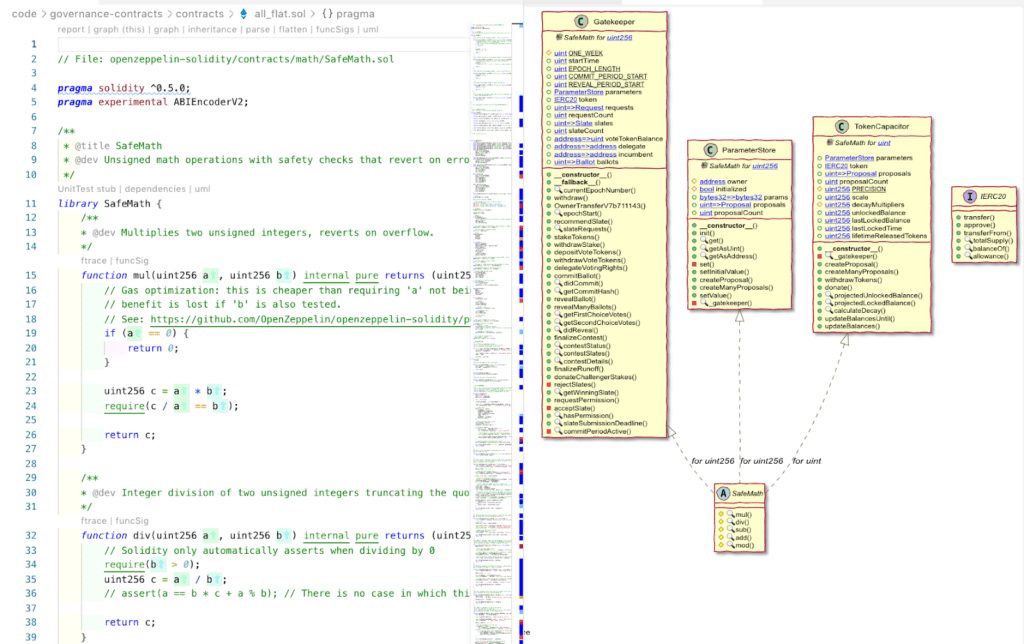
- Surya: Developed by ConsenSys, is a powerful tool for visualizing and analyzing the structure of smart contracts. It generates control flow graphs, inheritance trees, and function call traces, significantly aiding in manual inspections. Surya also flattens contracts and provides detailed summaries of contracts and their methods, making it an invaluable tool for understanding and auditing smart contracts.
In-Depth Static Analysis: Uncovering Code Vulnerabilities
Static analysis is crucial for identifying potential vulnerabilities in smart contracts. Static analysis involves examining the code without executing it. This step is essential for finding common issues and ensuring the security and reliability of smart contracts. Here are the top tools that excel in these processes:
Tools for Static Analysis
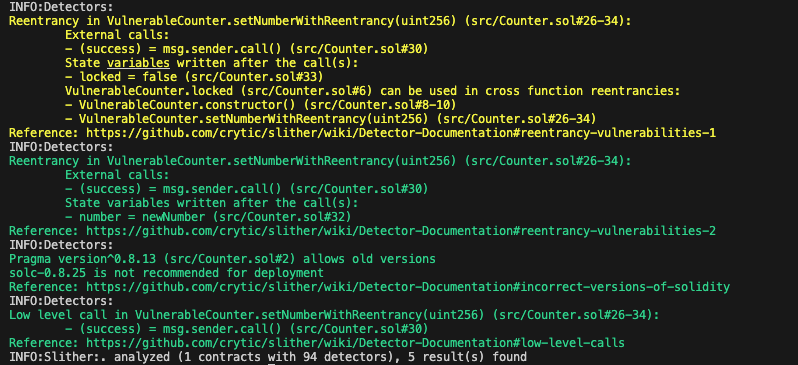
- Slither: This is a powerful static analysis tool designed for Solidity and Vyper smart contracts. Developed by Trail of Bits, it offers a suite of 94 built-in detectors to identify vulnerabilities such as reentrancy, uninitialized state variables, and suicidal functions. Slither stands out for its low false-positive rate and fast execution time, often taking less than a second per contract. Additionally, it integrates seamlessly with CI/CD pipelines, making it an invaluable tool for continuous security testing.
-
- Usage : slither .
-
- Securify 2.0: Supported by the Ethereum Foundation and ChainSecurity, offers advanced analysis for Solidity smart contracts. It uses context-sensitive analysis to identify 37 different types of vulnerabilities, from uninitialized state variables to reentrancy. Securify 2.0’s novel analysis techniques ensure thorough security assessments, making it a reliable tool for developers aiming to enhance their contract security.
- Rattle: Developed by Crytic, the blockchain arm of Trail of Bits, provides a static analysis framework specifically for deployed smart contracts. It parses EVM byte strings to produce a control flow graph of the contract, optimizing the SSA instructions by removing redundant opcodes like DUP, SWAP, PUSH, and POP. This optimization trims over 60% of EVM instructions, resulting in a much more readable and user-friendly interface. Rattle is particularly useful for understanding the structure and behavior of smart contracts, enhancing the ability to audit and interact with them effectively.
- Usage: python3 rattle-cli.py –input
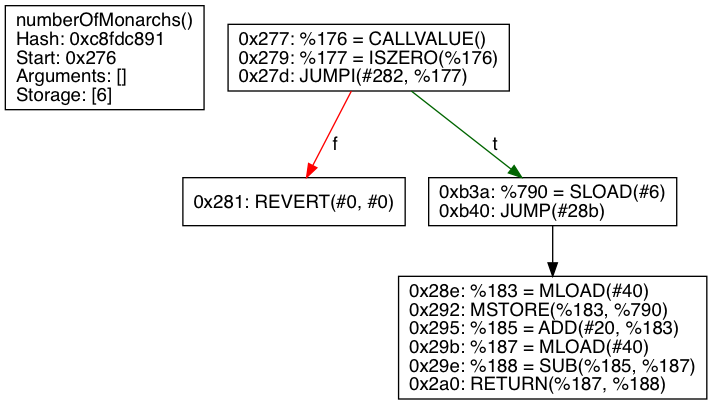
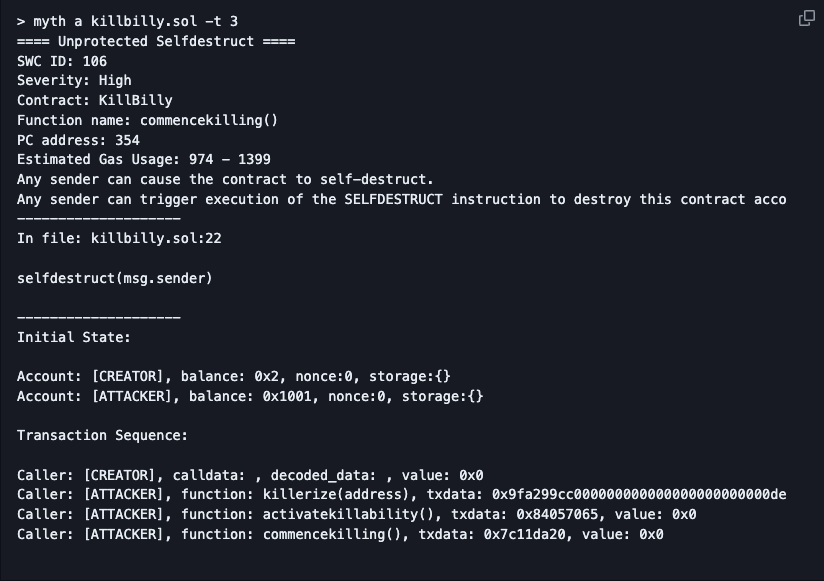
- Mythril: is a versatile security analysis tool for EVM bytecode, developed as part of the MythX security analysis suite by ConsenSys. It uses symbolic execution, SMT solving, and taint analysis to detect a wide range of security vulnerabilities. Mythril can be used for both static and dynamic analysis, making it a comprehensive tool for auditing smart contracts on Ethereum, Hedera, Quorum, Vechain, Rootstock, Tron, and other EVM-compatible blockchains. When integrated with MythX, developers benefit from additional IDE plugins, instructional documentation, and command line tools, enhancing their security capabilities.
- Usage: myth analyze <solidity-file>
Mutation Testing: Enhancing Test Suite Robustness and Coverage
Mutation testing introduces small, controlled changes (mutations) to the source code to evaluate the effectiveness of the test suite. It helps identify areas where tests may be inadequate or missing, ultimately enhancing the thoroughness of test coverage. Here are some of the top tools used for mutation testing in smart contracts:
Tools for Mutation Testing
-
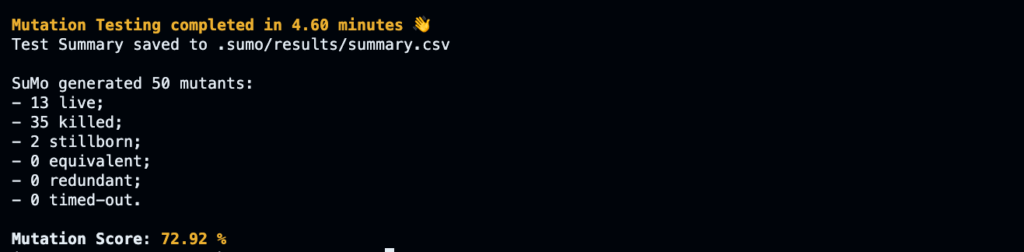
- SuMo: This is a mutation testing tool designed for Solidity smart contracts, running in a NodeJS environment. It supports Truffle, Hardhat, Brownie, and Foundry projects. SuMo features 25 Solidity-specific mutation operators and 19 traditional operators, generating a wide range of mutated codes to evaluate the robustness of test suites. It provides detailed reports and a mutation score to assess the effectiveness of the tests.
- Usage: npm sumo list, npx sumo test
- SuMo: This is a mutation testing tool designed for Solidity smart contracts, running in a NodeJS environment. It supports Truffle, Hardhat, Brownie, and Foundry projects. SuMo features 25 Solidity-specific mutation operators and 19 traditional operators, generating a wide range of mutated codes to evaluate the robustness of test suites. It provides detailed reports and a mutation score to assess the effectiveness of the tests.
- Vertigo-rs: Developed by RareSkills (fork of Joran Honig’s vertigo testing framework with added support for Foundry), is a mutation testing framework that works specifically with Foundry projects. It mutates smart contract files and runs tests to see if the introduced mutations survive. Vertigo-rs focuses on enhancing the quality and effectiveness of test suites by generating mutants and checking if the tests can detect potential bugs, providing an objective metric called the mutation score.
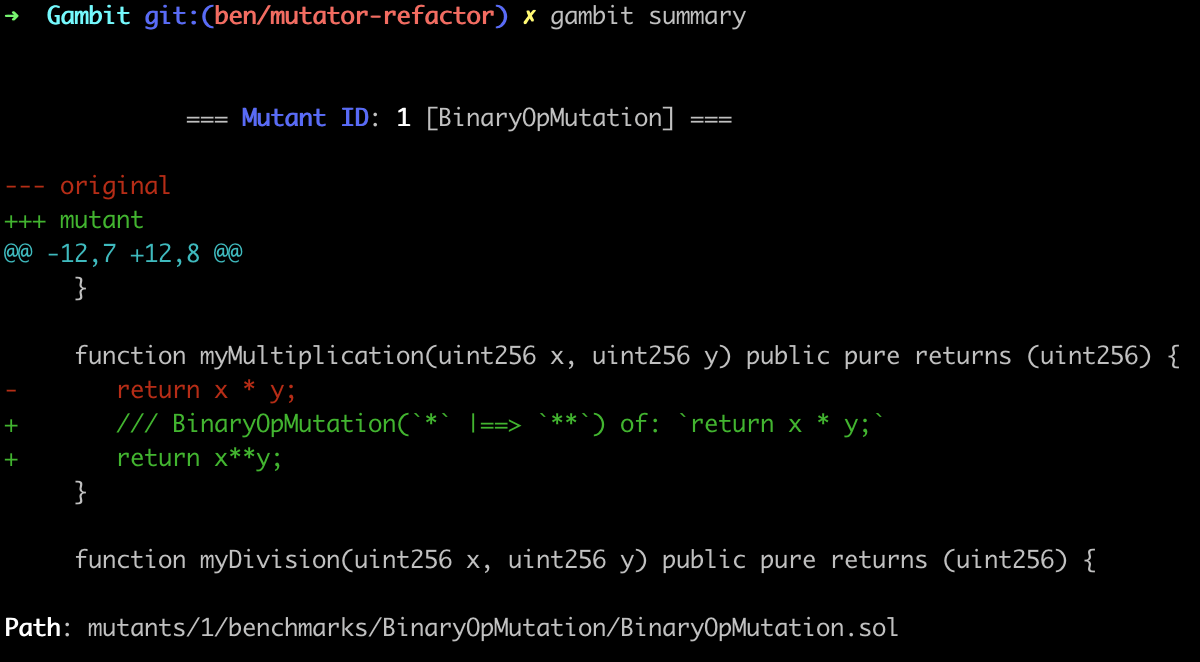
- Certora Gambit: Is a mutation system for Solidity developed by Certora. It generates mutants by applying predefined syntax transformations to Solidity code, which can then be used to evaluate the robustness of test suites or formal verification specifications. Gambit helps in identifying potential bugs and improving the overall quality of the test suite.
- Usage: gambit mutate –filename <file.sol>
Fuzzing and Invariant Testing: Ensuring Comprehensive Contract Security
Fuzzing and invariant testing are dynamic analysis techniques that help identify vulnerabilities in smart contracts by executing the code with unexpected inputs and verifying specific properties, respectively. These methods ensure that smart contracts behave correctly under various conditions and edge cases. Here are the top tools used for fuzzing and invariant testing:
Tools for Fuzzing & Invariant Testing
- ConsenSys Diligence Fuzzing: This is a powerful fuzz testing tool that identifies flaws in smart contracts. Part of the ConsenSys Diligence security suite, it offers both a CLI tool for local fuzzing and a cloud-based dashboard for organizing and monitoring fuzzing activities. The tool leverages smart contract annotations written in Scribble to specify security properties and constraints, checking these properties against random inputs to find violations.
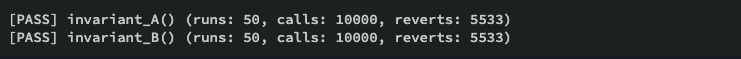
- Foundry Invariant Testing: Foundry is a robust smart contract development tool built with Rust, featuring fast fuzz testing and invariant testing capabilities. It handles project dependencies, compiles projects, runs tests, and deploys contracts. Foundry’s handler-based testing method is particularly useful for performing invariant tests involving cross-contract interactions, allowing developers to ensure that specific conditions hold true across various scenarios.
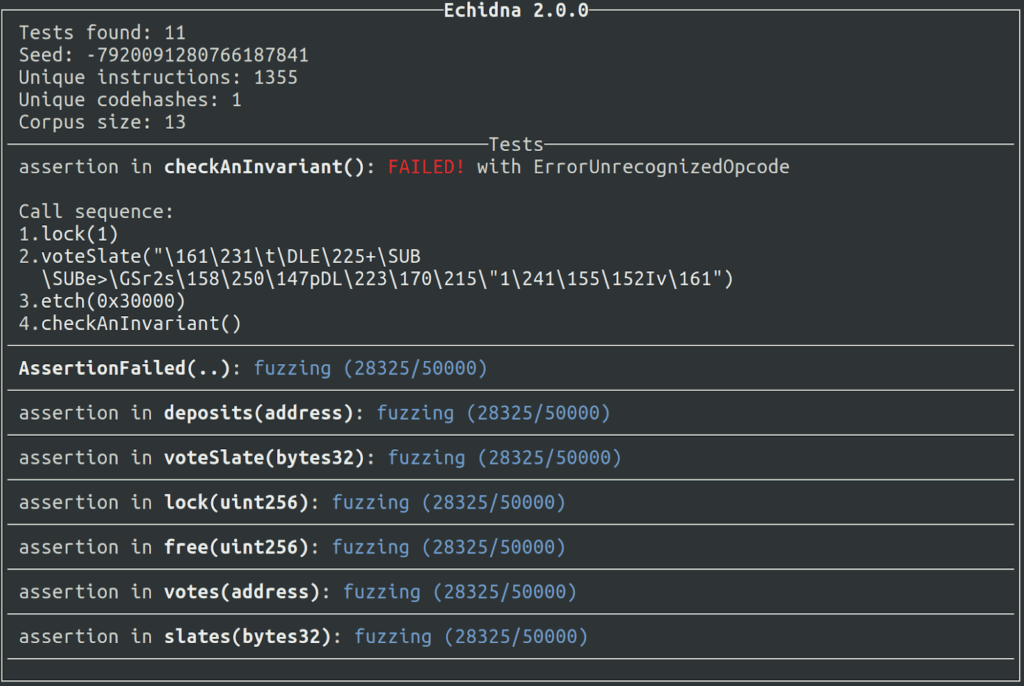
- Echidna: This is a sophisticated fuzzing and property-based testing tool for Ethereum smart contracts, written in Haskell. It uses grammar-based fuzzing campaigns based on a contract’s ABI to falsify user-defined predicates or Solidity assertions. Echidna generates random sequences of contract calls to test against predefined invariants, providing a high level of confidence in the contract’s safety.
- Usage: echidna myContract.sol
- Harvey: Employs greybox fuzzing to detect bugs and security vulnerabilities in smart contracts. It extends traditional fuzzing techniques with methods to predict new inputs likely to cover new paths or reveal vulnerabilities. Harvey’s targeted and demand-driven approach increases its effectiveness in achieving high coverage and detecting vulnerabilities.
Formal Verification and Symbolic Execution: Ensuring Smart Contract Integrity
Formal verification and symbolic execution are advanced techniques to ensure the correctness and security of smart contracts. These methods utilize mathematical proofs and symbolic reasoning to detect vulnerabilities and verify contract behavior against predefined specifications.
Tools for Formal Verification & Symbolic Execution
-
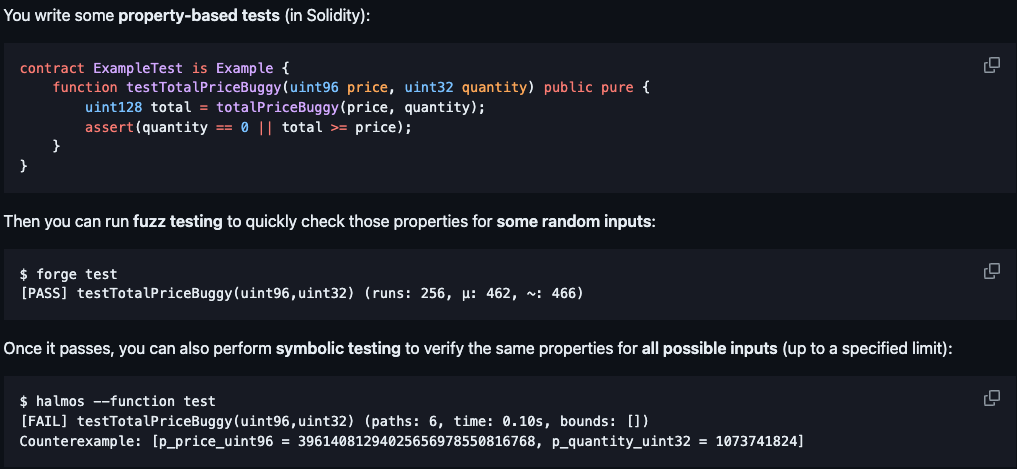
- Halmos: Developed by a16z, Halmos is an open-source symbolic execution tool designed for Ethereum smart contracts. Using symbolic methods and bounded model checking, Halmos can uncover vulnerabilities that traditional testing might miss. It explores all possible execution paths within a contract, ensuring comprehensive analysis and bug detection, thus bridging the gap between unit testing and formal verification.
- Certora Prover: This is a sophisticated formal verification tool that analyzes smart contracts against specifications written in Certora Verification Language (CVL). It combines static analysis and SMT (Satisfiability Modulo Theories) to detect cases where the contract’s behavior deviates from its specifications. By creating formal proofs, Certora Prover ensures that the smart contract adheres to desired properties, making it a powerful tool for eliminating bugs and vulnerabilities.

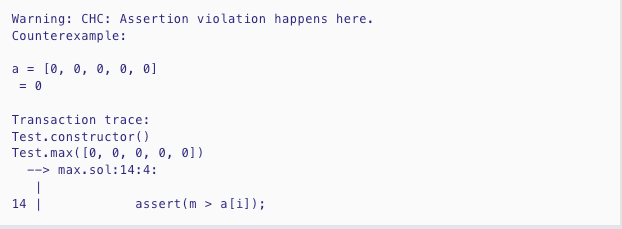
- Solidity SMTChecker: This is an integrated formal verification tool within the Solidity compiler (solc). It uses SMT and Horn solving to transform program logic into SMT statements, checking for assertion failures. By interpreting require and assert statements as formal specifications, SMTChecker ensures the contract’s correctness through bounded and unbounded model checking, providing developers with mathematical assurance of their code’s reliability.
- HEVM: This is a Haskell-based implementation of the Ethereum Virtual Machine (EVM) focused on symbolic execution, unit testing, and debugging of smart contracts. It uses SMT solvers like Z3 and CVC4 to prove the correctness of smart contracts, exploring all potential execution paths to find assertion failures and other vulnerabilities. HEVM’s integration with the foundry suite enhances its capabilities, making it a robust tool for contract verification.
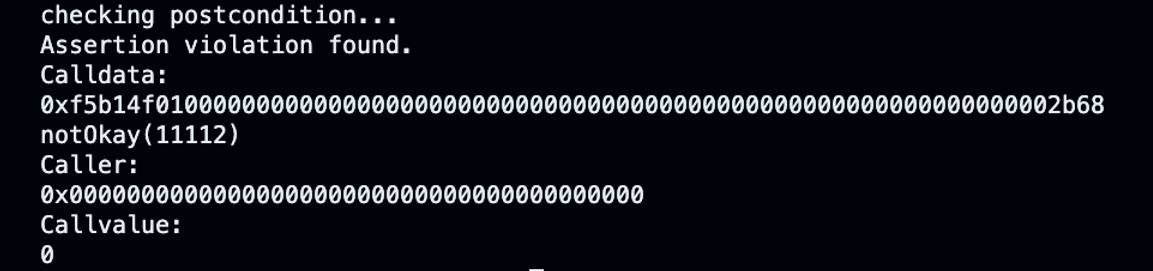
- Manticore: This is a versatile symbolic execution tool that analyzes smart contracts and binaries, exploring possible states and generating inputs to detect errors. It supports Ethereum smart contracts, Linux ELF binaries, and WASM modules. Manticore’s state management lifecycle and symbolic reasoning capabilities make it effective in finding complex bugs, providing a powerful tool for ensuring contract security
- Usage: manticore <path/to/file.sol>
Code Coverage Tools: Ensuring Comprehensive Testing
Code coverage tools are crucial for measuring the extent to which the source code of a program is executed during testing. By identifying untested parts of the code, these tools help developers ensure that their software is reliable, secure, and thoroughly tested.
-
Tools for Code Coverage
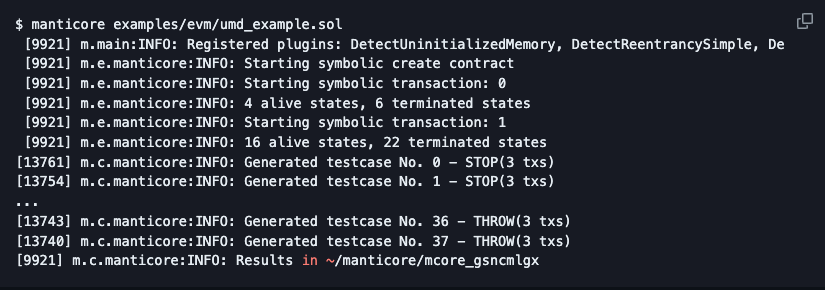
- Solidity-Coverage (Solcover): Commonly referred to as Solcover, is a popular tool for measuring the test coverage of Ethereum smart contracts written in Solidity. It helps developers identify untested paths in their contracts by automatically modifying the source code to include execution markers. Solcover generates detailed reports that highlight untested areas, making it easier for developers to ensure comprehensive testing. With advanced configuration options, including target testing and custom paths, Solcover offers a flexible and powerful solution for enhancing the reliability and security of smart contracts.
- Usage: npx hardhat coverage [command-options]
- Solidity-Coverage (Solcover): Commonly referred to as Solcover, is a popular tool for measuring the test coverage of Ethereum smart contracts written in Solidity. It helps developers identify untested paths in their contracts by automatically modifying the source code to include execution markers. Solcover generates detailed reports that highlight untested areas, making it easier for developers to ensure comprehensive testing. With advanced configuration options, including target testing and custom paths, Solcover offers a flexible and powerful solution for enhancing the reliability and security of smart contracts.
Manual Code Review: An Essential Component of Smart Contract Auditing
Automated tools such as Slither, Mythril and Echidna, have significantly enhanced the efficiency and scope of smart contract auditing. These tools are invaluable for swiftly identifying common vulnerabilities and saving time in the initial stages of the audit process. However, despite their strengths, automated tools are not a panacea. They have notable limitations, particularly when it comes to detecting complex issues such as asset lock, logical errors, or oracle manipulations. According to IEEE research, current security tools can only detect 8-20% of exploitable bugs, underscoring the necessity of manual code reviews.
The Importance of Manual Review
Human involvement is indispensable in the smart contract auditing process. While automated tools excel at identifying standard vulnerabilities and coding mistakes, they lack the contextual understanding and broader considerations that human auditors bring to the table. Manual reviews allow for a nuanced examination of the code, considering factors such as uncommon vulnerabilities, logical errors, and the impact of human and economic factors on the contract’s operation.
Manual code reviews provide a comprehensive approach to smart contract security by addressing areas that automated tools might miss. These reviews help in:
- Identifying Logical Errors: Automated tools might miss logical errors in the contract’s design. Human auditors can understand the intended functionality and ensure that the code aligns with the business logic.
- Gas Optimization Opportunities: Manual reviews can identify inefficient code that consumes excessive gas, providing suggestions for optimization.
- Assessing Code Architecture: Human auditors can evaluate the overall architecture of the contract, identifying potential weak points and suggesting improvements.
- Evaluating Coding Practices: Human reviewers can detect poor coding practices that might be technically correct but suboptimal or risky in practice.
Identifying Business Logic Issues
Manual code reviews are particularly effective at identifying business logic issues. These issues often arise from discrepancies between the intended functionality of the smart contract and its actual implementation. Human auditors can:
- Understand Intent: By grasping the intended use and business context, auditors can detect when the code deviates from expected behavior.
- Simulate Scenarios: Auditors can simulate various real-world scenarios to ensure that the contract behaves correctly under different conditions.
- Spot Edge Cases: Manual reviews help identify edge cases that might not be covered by automated tests, ensuring robust and reliable contract performance.
Tools for Efficient Reporting in Smart Contract Auditing
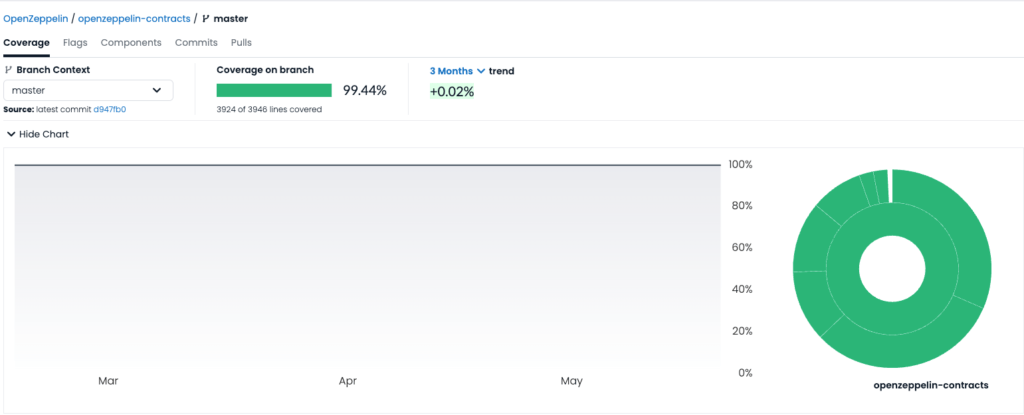
weAudit by Trail of Bits: weAudit is a collaborative code-reviewing tool designed for use within VSCode. Developed by Trail of Bits, it allows auditors to efficiently review code, take notes, and track bugs directly inside VSCode. Features include:
- Bookmarks for findings and notes.
- Tracking of audited files.
- Collaboration capabilities for sharing findings.
- Creation of detailed GitHub issues from within the tool.
weAudit helps streamline the process of bookmarking, annotating, and tracking code files, enhancing the efficiency and thoroughness of security audits.
- Usage:
“weAudit: New Finding from Selection” (shortcut: Cmd + J)
“weAudit: New Note from Selection” (shortcut: Cmd + K)
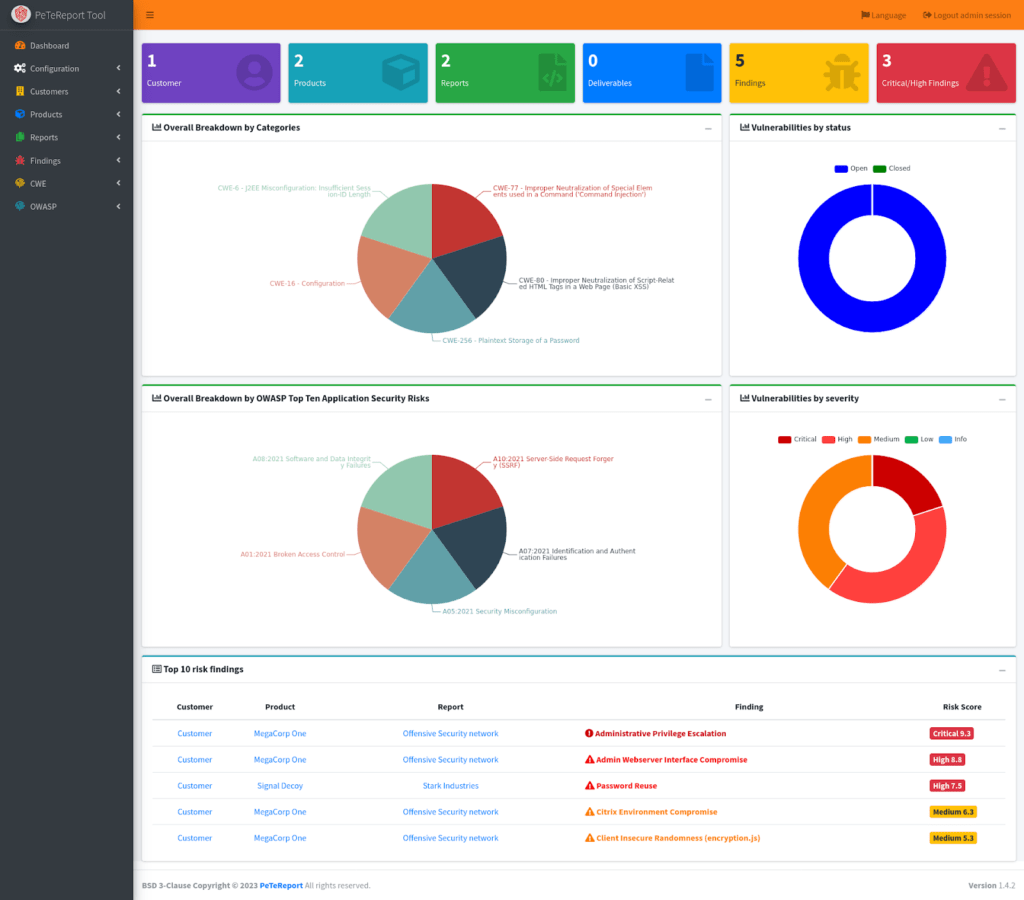
PeTeReport (PenTest Report): is an open-source application designed to assist pentesters and red teamers in writing and generating detailed vulnerability reports. Key features include:
- Customizable report outputs and templates.
- A findings template database.
- The ability to add appendices and attack flows to findings.
- Multiple report output formats (HTML, CSV, PDF, Jupyter Notebook, Markdown).
- Integration with DefectDojo and user management capabilities.
PeTeReport simplifies the reporting phase, allowing security researchers to focus on their findings rather than the administrative aspects of report creation.
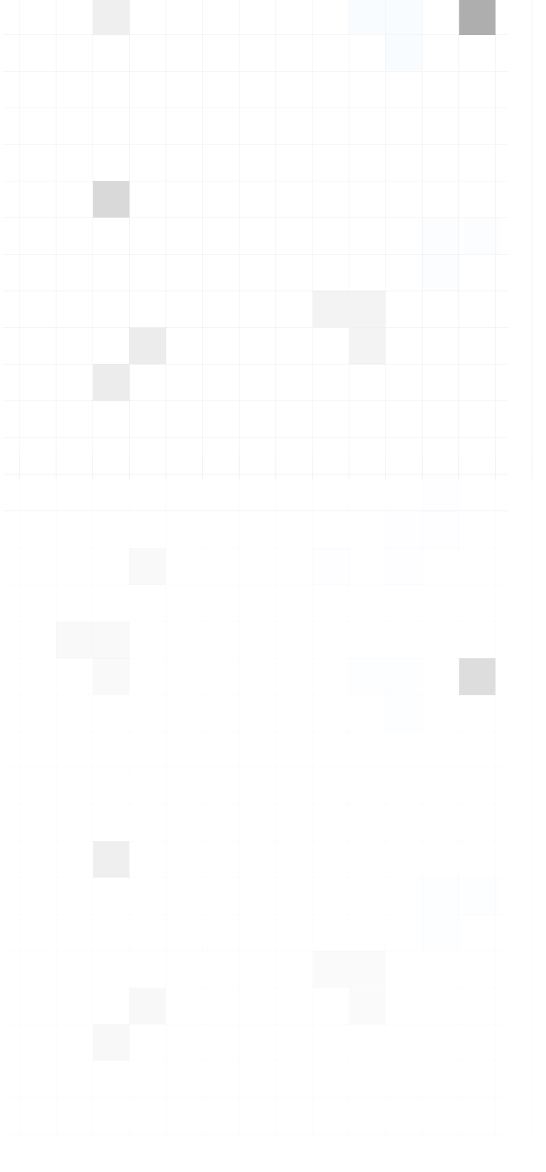
Quick Comparison of Smart Contract Auditing Tools
Overview: This table provides a concise comparison of various smart contract auditing tools. It highlights their key features, strengths, and limitations, offering a quick reference for developers and auditors to choose the appropriate tools for ensuring the security and reliability of smart contracts.
Tool |
Key Features |
Strengths |
Limitations |
| Solidity Visual Auditor (SVA) | Visual representation of smart contracts | Enhances understanding of structure and flow, integrates with VSCode | Limited to visual representation, no direct vulnerability detection |
| Surya | Control flow graphs, inheritance trees, function call traces | Comprehensive visual analysis, useful for manual inspections | Requires Graphviz for graph generation, less intuitive compared to SVA |
| Slither | 94 built-in detectors, fast execution, CI/CD integration | Low false-positive rate, fast analysis, extensive detection capabilities | Generates some false positives, limited to Solidity and Vyper |
| Securify 2.0 | Context-sensitive analysis, 37 vulnerability detectors | Thorough security assessments, detailed reports | Not actively maintained, tedious installation |
| Rattle | Parses EVM byte strings, control flow graph, optimizes SSA instructions | Improves readability of EVM instructions, useful for auditing | Limited to bytecode analysis, misses some business logic vulnerabilities |
| Mythril | Symbolic execution, SMT solving, taint analysis | Versatile, supports multiple EVM-compatible blockchains, detailed vulnerability detection | Slow analysis, potential false positives |
| SuMo | Mutation testing for Solidity, NodeJS environment support | Evaluates test suite robustness, supports multiple development frameworks | Time-consuming for large projects |
| Vertigo-rs | Mutation testing with Foundry support | Enhances test suite quality, provides mutation score | Limited to Foundry projects, manual test execution required |
| Certora Gambit | Mutation testing for Solidity, generates mutants | Enhances test suite quality, improves robustness | Manual testing required, limited documentation |
| ConsenSys Diligence Fuzzing | Fuzz testing with CLI and cloud-based dashboard, smart contract annotations | Effective bug detection, scalable testing capability, cloud and local testing support | Complex setup, subscription-based, concerns over data privacy |
| Foundry Invariant Testing | Rust-built, fast fuzz testing and invariant testing | Fast testing, useful for cross-contract interaction tests | Manual input range bounding required |
| Echidna | Property-based testing, grammar-based fuzzing campaigns | Powerful fuzzer, easy to use, comprehensive security testing | Slow for large contracts, limited Vyper support |
| Harvey | Greybox fuzzing, predicts new inputs to cover new paths | Effective in detecting vulnerabilities, increases coverage | May not generalize to all smart contracts, potential for systematic errors |
| Halmos | Symbolic execution, bounded model checking | Effective bug detection, explores all execution paths, bridges gap between unit testing and formal verification | Still in development, may not find all bugs, slow for complex contracts |
| Certora Prover | Formal verification, static analysis, SMT solving | Eliminates bugs through formal proofs, ensures contract adheres to specifications | Computationally expensive, commercial tool |
| Solidity SMTChecker | Integrated with Solidity compiler, SMT and Horn solving | Ensures contract correctness, provides mathematical assurance, part of Solidity compiler | Experimental, may produce false positives, limited by finite path exploration |
| HEVM | Symbolic execution, unit testing, debugging | High performance, effective symbolic testing, integrates with dapptools | Complex usage, slow for large codebases |
| Manticore | Symbolic execution for smart contracts and binaries | Versatile, effective in finding complex bugs, supports various software types | Memory-intensive, potential conflicts with other CLI tools, slow for large programs |
| Solidity-Coverage (Solcover) | Measures test coverage, generates detailed reports | Simplifies test coverage tracking, supports advanced configurations | Limited to Solidity, advanced options depreciated |
Expanding Your Smart Contract Auditing Toolbox
- Solodit: Best for Smart Contract Security Research
Solodit is a valuable resource for auditors to learn about vulnerabilities and security breaches. It aggregates over 8,000 security vulnerabilities and bounties from top security firms and researchers worldwide, providing detailed reports and advanced search and filtering tools.
- Glider: Revolutionizing Web3 Auditing and Security Analysis
Glider is a powerful tool for advanced query-based smart contract analysis, specifically designed for EVM-based blockchains. It introduces variant analysis, enabling security researchers to identify and address vulnerabilities at scale, significantly reducing false positives and enhancing the efficiency of security audits.
Comprehensive Resources for Smart Contract Auditing Tools
For a more extensive list of smart contract security auditing tools, explore resources like GitHub and Alchemy. These resources provide detailed information on various tools that can aid in different aspects of smart contract auditing and security.
- GitHub’s Smart Contract Auditor Tools and Techniques: An extensive resource compiled by user @shanzson, offering links and information on various auditing tools.
- Alchemy’s List of 111 Best Solidity Tools: A curated list of the best tools for Solidity development and auditing.
Conclusion: Fortifying Smart Contracts with Comprehensive Auditing
Ensuring the security and integrity of smart contracts is essential in the blockchain landscape. This article has showcased various tools that enhance the auditing process, from static analyzers like Slither to advanced formal verification tools like Certora Prover.
Automated tools provide valuable insights but cannot replace the critical role of manual code reviews. Human auditors identify complex issues that tools might miss, ensuring thorough security.
At BlockApex, we combine cutting-edge tools with expert manual reviews to deliver reliable security assessments. By leveraging these tools and methodologies, BlockApex ensures the blockchain community can build secure and robust smart contracts, fostering trust and innovation in the decentralized world.
Read More:
Advantages And Disadvantages Of Smart Contracts
Top Industry Leading Smart Contract Auditing Tools