It was through a simple PDF and a fake job offer that the biggest heist in crypto history took place in 2022 when Ronin Bridge lost an astounding $624 million. The year 2023 saw a 65.3% increase in Web3 security incidents compared to 2022, with 110 new incidents recorded.
In the burgeoning world of decentralized finance (DeFi), non-custodial wallets have become the cornerstone of individual financial sovereignty. However, with great power comes great responsibility — especially in safeguarding these wallets from the rising tide of scams, hacks, and phishing attempts. As a Web 3.0 security company, we’ve seen firsthand how these threats have evolved, often preying on human errors and misinformation.
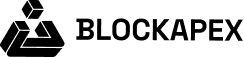
In today’s digital world, phishing emails are a common but dangerous threat. They trick individuals into revealing personal information or downloading malware, leading to potential financial losses or data breaches. According to Zero Hour Technology’s statistics, a total of 506 security incidents and cumulative losses reaching $11 billion in 2023, there’s a clear upward trend in the frequency and impact of Web3 security breaches. Recently, a series of phishing emails imitating reputable sources like CoinTelegraph, Token Terminal and Wallet Connect have led to significant financial losses over $2.6 million so far (Attacker Address). It’s crucial to recognize these deceptive emails to protect yourself and your information.
The Web of Social Engineering Scams:
It was through social engineering that the crypto VC Bo Shen lost a whopping $42 million in November 2022 and Chris Larsen, chairman of Ripple, lost approx. $112.5 million in January 2024. These scams, designed to manipulate or deceive users into divulging confidential information or performing actions against their interests, include:
- Phishing Attacks: Beyond emails, these can manifest through fake websites, social media messages, and even direct messages on platforms like Discord or Telegram, mimicking legitimate entities to steal credentials or private keys.
- Baiting Scams: Similar to phishing, baiting involves offering something enticing, like a free airdrop or access to exclusive digital assets, to trick individuals into giving up sensitive information or downloading malware.
- Pretexting: Here, the attacker creates a fabricated scenario or pretext to collect personal data. In the context of Web3, this might involve impersonating customer support to “resolve issues” with your wallet.
- Quid Pro Quo: Offers of a service or benefit in exchange for information or access. For example, someone might offer to “increase your wallet security” if you provide them with your seed phrase.
- Tailgating or Piggybacking: Though more physical in nature, this can also occur digitally when unauthorized users gain access to restricted areas or information by following someone who’s authorized. In Web3, this might translate into exploiting trust relationships within communities to spread malware or scams.
Airdrops as a Double-Edged Sword:
Airdrops, while a popular method for projects to reward community members or promote token distribution, can also serve as a hook for scammers. The allure of free tokens can lead users to lower their guards, making them susceptible to scams such as:
- Fake Airdrop Websites: Sites that mimic legitimate projects, asking users to connect their wallets to claim tokens, only to drain those wallets instead.
- Permission Scams: Airdrops that require users to grant permissions that are overly broad or unnecessary, potentially allowing scammers to access wallets or execute transactions without further consent.
Safeguarding Your Wallet
Non-custodial wallets empower users with complete control over their digital assets, eliminating the need for intermediaries. However, this control also means that the security of the wallet lies entirely in the hands of the user. Common vulnerabilities often stem from weak security practices, such as poor password management or falling prey to phishing scams. In 2023, private key exploits emerged as the most detrimental hacks for the crypto space, causing losses totaling $555 million.
Understanding Sensitive Actions
- MetaMask Connect: Connecting your MetaMask wallet to a website or application is a highly sensitive action. It can grant the site access to your wallet and transactions.
How Sensitive Information is Exposed
- Access Granted through Airdrops: In the excitement of an airdrop, users might hastily connect their wallets to unverified sites, inadvertently granting malicious actors access to their assets.
Know your signatures
The process of verifying signatures or contracts before engaging with them involves a few crucial steps. Here’s how you can ensure the authenticity of the contracts you interact with:
- Copy the Address: Whenever you’re prompted to sign a transaction or engage with a contract, the first step is to copy the address from the signature request.
- Use a Block Explorer: Navigate to a reliable block explorer that corresponds with the blockchain network you’re using. For Ethereum transactions, Etherscan is the go-to platform; for Binance Smart Chain (BSC) activities, BSCScan is appropriate; and for Polygon-based transactions, Polygonscan will serve your needs.
- Enter the Address: Paste the copied address into the search bar of the chosen block explorer. This action will fetch the details associated with the address.
- Verify the Contract: Upon searching, you’ll be presented with information about the contract or address. This is where you need to exercise due diligence:
- Authenticity Check: Determine if the contract address matches the official address provided by the project. Legitimate projects often list their contract addresses on their official websites or verified social media channels.
- Identify the Attacker: If the address doesn’t match the project’s official addresses or has been flagged by the community, it might belong to an attacker. Look out for any warnings or comments on the block explorer page that indicate malicious activity associated with the address.
Mitigating Risks
- Revoke Unnecessary Access: Regularly review and revoke permissions from sites you no longer trust or use. Tools within MetaMask and other wallets allow you to manage these permissions.
- Use Spam Trackers: Implement spam tracker tools or snaps that alert you to potential phishing sites or malicious airdrops. These tools can provide an additional layer of security by analyzing and flagging risky connections. Some recommended tools include:
- MetaMask Phishing Detector: Integrated into the MetaMask wallet for direct alerts.
- PhishFort: Specifically tailored for crypto users to identify phishing threats.
- CryptoScamDB: An open-source database that tracks known phishing sites in the crypto space.
- Netcraft Extension: A browser extension offering broad protection against phishing.
- Norton Safe Web: Scans and rates website safety, including phishing risk assessment.
Understanding Phishing Emails
Phishing emails are deceptive messages designed to appear as if they are from trustworthy sources. These emails often prompt you to take immediate action, such as clicking a link, downloading an attachment, or providing personal information. The goal of the attacker is to steal sensitive data, infiltrate networks, or install harmful software on your device.
Common Characteristics of Phishing Emails
- Suspicious Email Addresses: Check if the sender’s email address matches the organization they claim to represent. Look out for subtle misspellings or odd domain names.
- Generic Greetings: Phishing emails often use vague greetings like “Dear Customer” instead of personalized introductions.
- Urgent Requests: Be wary of emails creating a sense of urgency or offering too-good-to-be-true rewards.
- Grammar and Spelling Mistakes: Reputable organizations usually send well-written emails. Poor grammar and spelling can be a red flag.
- Mismatched Links: Hover over links to see the actual URL. If it doesn’t match the context or seems suspicious, don’t click it.
- Attachments: Be cautious of unexpected attachments, especially from unknown senders.
How to Verify Email Authenticity
Using Technical Tools
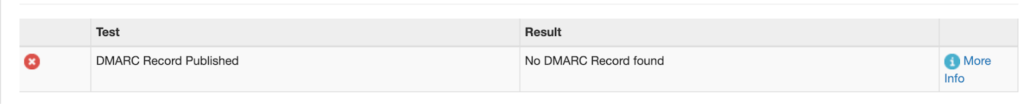
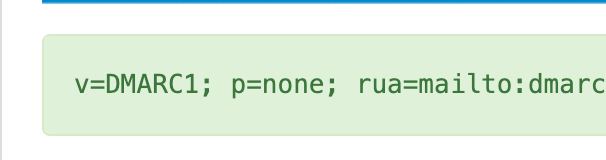
DMARC Records: Use tools like MXToolbox to check the DMARC record of the sending domain. If it’s not published or set to a lenient policy like the flag “p” is set to “none”, the domain might be spoofed.
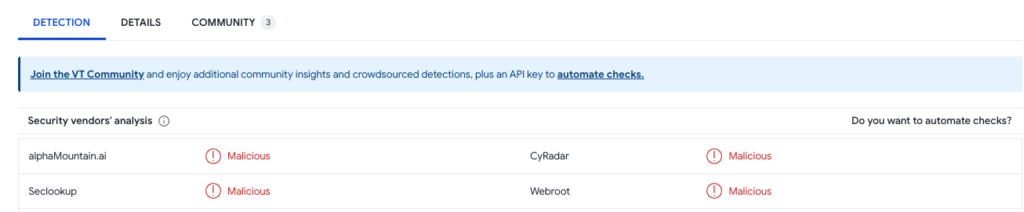
Link Verification: Copy the link from the email (Don’t open it) and use services like VirusTotal to check its safety. This helps avoid accessing potentially harmful websites.
Fake Mailer Testing: Test the email domain with a fake mailer sending site to see if the domain can be spoofed, indicating potential risks.
Use of Antivirus: Use renowned antivirus software to scan your system for potential malware.
Simple and Effective Tips to Identify Phishing Emails
Spam Filters: Use your email client’s built-in spam filters and consider third-party services for better control.
Personal Information: Never share sensitive personal information, like passwords or bank details, via email.
Verify Independently: If an email seems suspicious, contact the sender through a different method, like a phone call, to confirm its authenticity.
Measures That You Must Take
- Unlike SEC, always enable 2FA authentication. It is more secure than using a strong and long password. 2FA requires a second form of identification beyond just the password. This means even if a hacker obtains your password, they can’t access your account without also having the second factor.
- Never open any shortened links that you receive. And always check out any link that you receive that contains an authentic source.
- Pay attention to the extensions of the file that you receive, check whether they are executable or not. Never open any executable file
- Executable extensions include .exe, .elf, .app, .vb, .iso, .sh, .bat
- List is available here https://aerorock.co.nz/list-of-executable-file-extensions-windows/
Conclusion: Staying Safe and Informed
Remaining vigilant and informed is your best defense against phishing emails. Always approach unsolicited emails with caution and utilize available tools to verify their authenticity. In the digital age, where cyber threats are evolving, education and awareness are key.
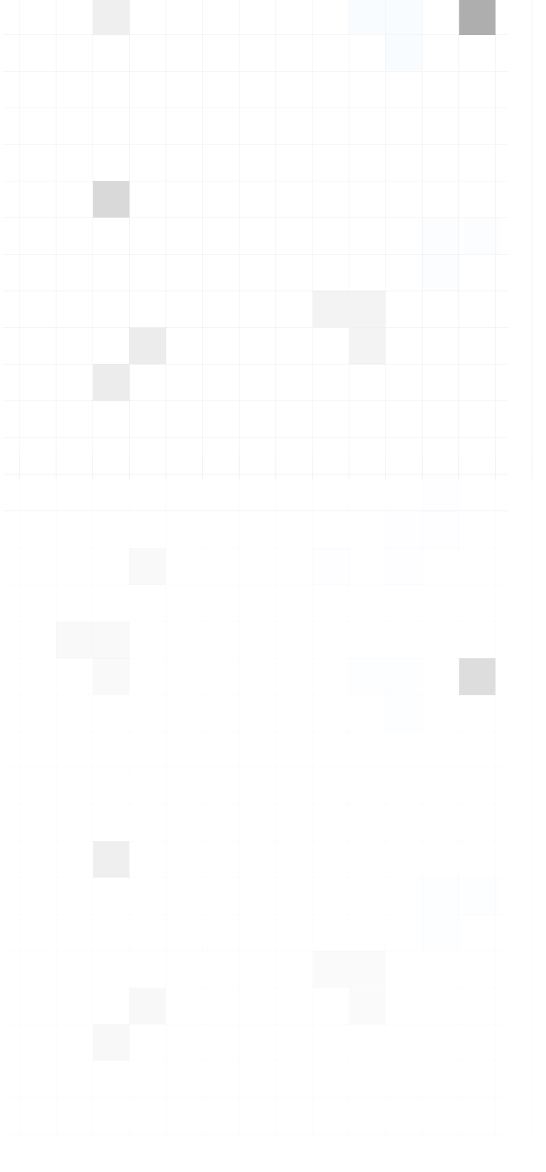
For added protection, consider consulting with cybersecurity experts like BlockApex. We specialize in blockchain security and provide services like DApp pentesting, actively looking for and addressing such security issues. Stay safe and informed, and let’s work together to create a more secure digital environment.