The DeFiGeek Community (DFGC), established in February 2021, is a diverse and growing group dedicated to the development of decentralized finance (DeFi) applications and middleware that contribute to the Web3 era. With a membership that includes developers and enthusiasts alike, DFGC aims to create a hub for sharing accurate industry information and fostering collaboration. Among its projects are the Yamato Protocol, a crypto-backed stablecoin pegged to the Japanese yen (JPY), and the planned Yorozu, a peer-to-peer lending Dapp. As the community works towards becoming a decentralized autonomous organization (DAO), it emphasizes fluidity and the elimination of authority to allow for independent leadership and innovation.
Hack Impact
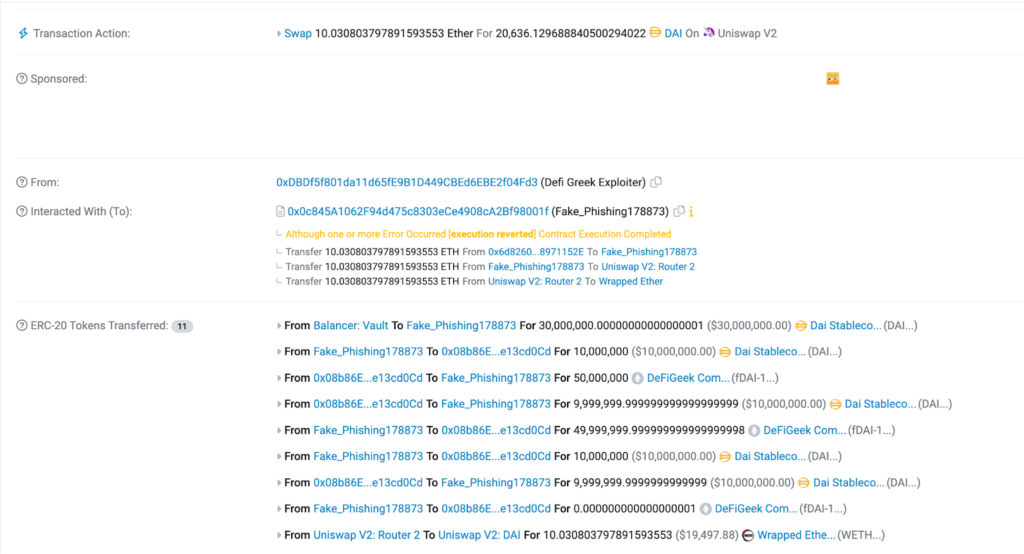
On Apr 17, 2023, the DeFiGeek Community fell victim to a security breach in which an attacker exploited a flash loan vulnerability, causing the loss of 10 ETH (valued at over $20,000) from their DeFiGeek Community Pool Dai (fDAI-102). The community has also committed to covering the lost funds through its treasury, mitigating the financial impact on its members.
Transactions Involved
Attack Tx hash: 0xa32c84ad09369880dfbdf01bcacc2de632ab8c49d97c33ef695fd0
Attacker address: 0xDBDf5f801da11d65fE9B1D449CBEd6EBE2f04Fd3
Attack Contract: 0x0c845a1062f94d475c8303ece4908ca2bf98001f
DeFiGeek Community Pool Dai (fDAI-102): 0x08b86e750ff8c816d8af
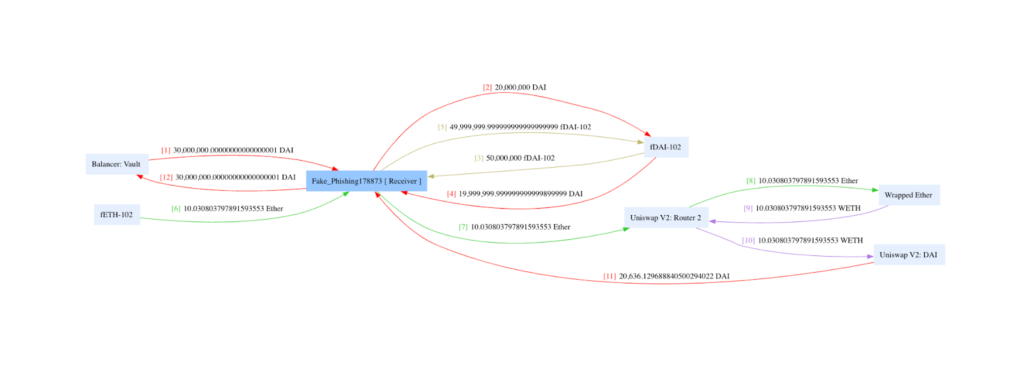
Fund’s Flow
Hack Explained: A Technical Breakdown
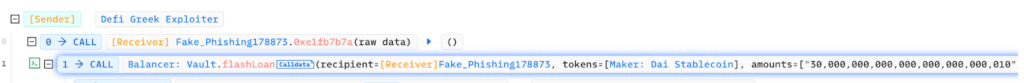
Obtain a flash loan
The attacker took out a flash loan from Balancer: Vault, acquiring a large amount of DAI (30,000,000 DAI) to exploit the DeFiGeek Community Pool vulnerability.
Interaction with the DeFiGeek protocol
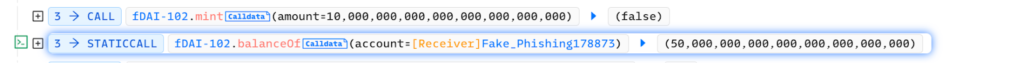
The attacker started interacting with the DeFiGeek protocol, sending 10M DAI to the protocol and receiving 50M fDAI-1 tokens in return, potentially manipulating the exchange rate between DAI and fDAI-1.
Further manipulation of token balances
The attacker continued to send DAI and fDAI-1 tokens back and forth between their own address and the DeFiGeek protocol, potentially exploiting the vulnerability in the protocol to skew the exchange rate further in their favor. This included sending approximately 10M DAI and 50M fDAI-1 back to the protocol and receiving approximately 10M DAI in return.
Trading on Uniswap
The attacker traded 10.03 WETH ($19,497.88) on Uniswap V2, obtaining 20,636.13 DAI ($20,636.13).
Profit extraction
With the manipulated exchange rate now in their favor, the attacker likely used their acquired fDAI-1 tokens to withdraw more DAI than they initially deposited
Repay the flash loan
The attacker returned the initial 30,000,000 DAI to Balancer: Vault, closing the loop on the flash loan.the attacker made a profit of 10 ETH, which is worth more than $20,000 at the time of the attack
Smart Contract Flaw
The contract was subject to a vulnerability that allowed an attacker to exploit the system and make a profit. The flaw in the smart contract was related to an improper handling of the collateral factor (CF) and borrow cap, which the attacker took advantage of by borrowing a large amount of funds and interacting with the protocol in a specific way. This enabled the attacker to manipulate the exchange rate between DAI and fDAI-1 tokens, ultimately making a profit at the expense of the protocol.
In response to the attack, DeFiGeek initially set a zero supply cap for the unused token pool, but this measure was insufficient to prevent the exploit. To fully mitigate the vulnerability and prevent similar attacks in the future, DeFiGeek set the collateral factor (CF) and borrow cap to zero for the unused token pool. This action effectively disables the ability to use the problematic asset for borrowing or providing collateral, eliminating the possibility of an attacker exploiting the same flaw again. By setting the CF and borrow cap to zero, DeFiGeek secures the protocol against similar attacks., ensuring the safety of its users’ funds.
Mitigation and Recommended Practices
- Conduct comprehensive audits for business logic vulnerabilities: Ensure that all possible vulnerabilities are identified and addressed. Create thorough test cases to prevent the exploitation of flash loans or other potential attack vectors.
- Prioritize internal state changes: When updating balances or invoking internal functions, always prioritize these actions before calling external code to minimize the risk of malicious actors taking advantage of the contract’s state.
- Regularly monitor for suspicious activity: Keep an eye out for any unusual deposits or transactions that could indicate fraudulent activity or arbitrage opportunities. Implement mechanisms to detect and prevent such activities from taking place.
- Implement secure coding practices: Develop and follow secure coding guidelines and best practices to minimize vulnerabilities in your smart contracts. Encourage the use of secure coding principles among developers and ensure regular code reviews to detect potential security issues.
- Engage in third-party security audits: Seek external security audits from reputable firms to identify and address any vulnerabilities that may have been missed during internal reviews.
Conclusion
The DeFiGeek Community hack serves as a reminder of the importance of robust security measures and best practices in the rapidly evolving DeFi landscape. As the sector continues to grow and attract more users, it is crucial to prioritize security and implement comprehensive audits, secure coding practices, and continuous monitoring for suspicious activities.
Additionally, fostering a security-conscious culture among developers and community members will help ensure that all parties involved remain vigilant in safeguarding against potential vulnerabilities and exploits. One of the recommended approaches to mitigating such risks is to engage third-party security audits from reputable firms, such as blockapex.io, to ensure that all possible vulnerabilities are identified and addressed promptly. By staying proactive and vigilant, the DeFi community can continue to innovate and thrive in a secure and reliable environment.
Explore other Hack Analyses: